
Since 1986 • 40 years of continuous development
Rz V7.zip Download -
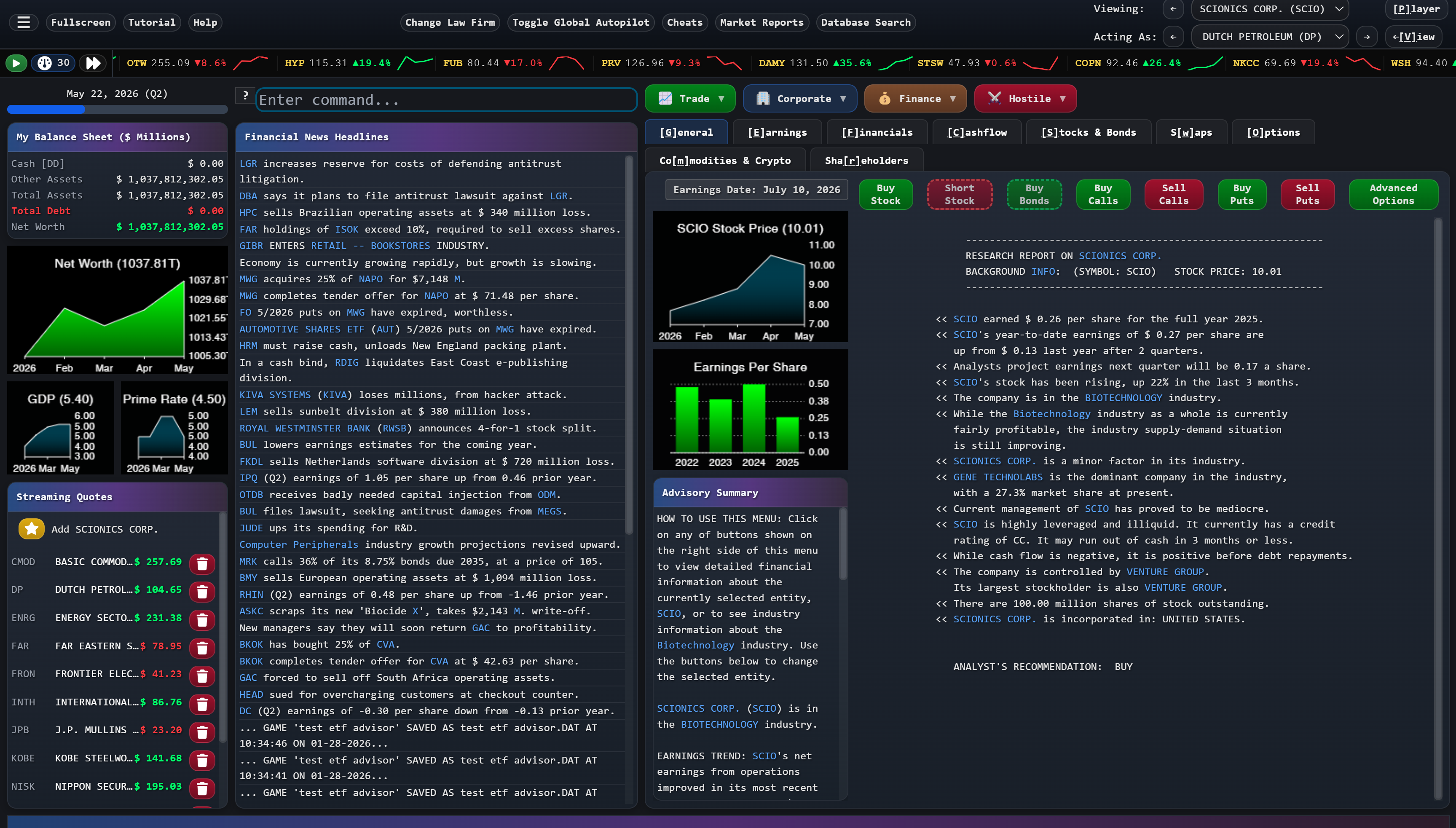
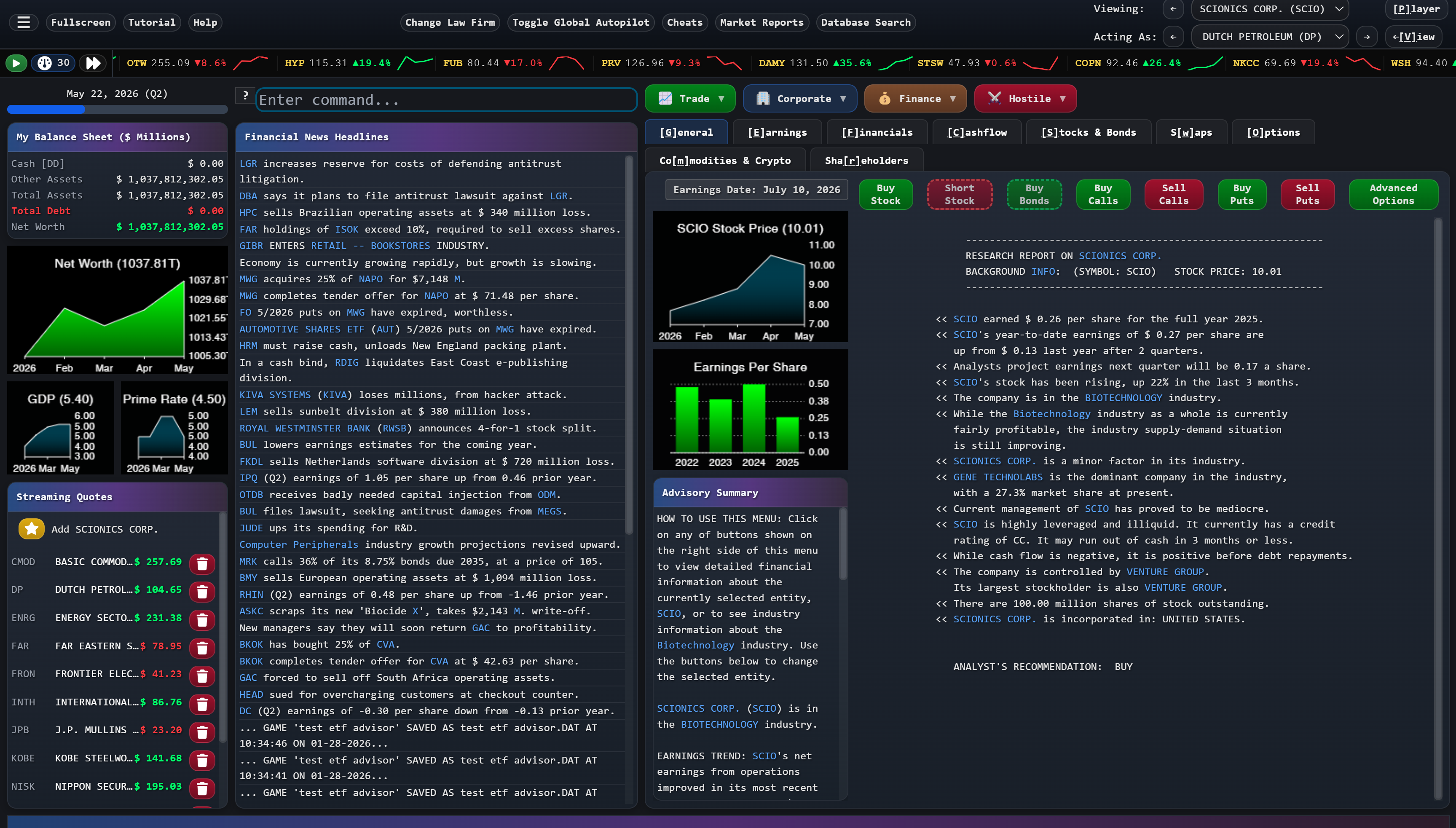
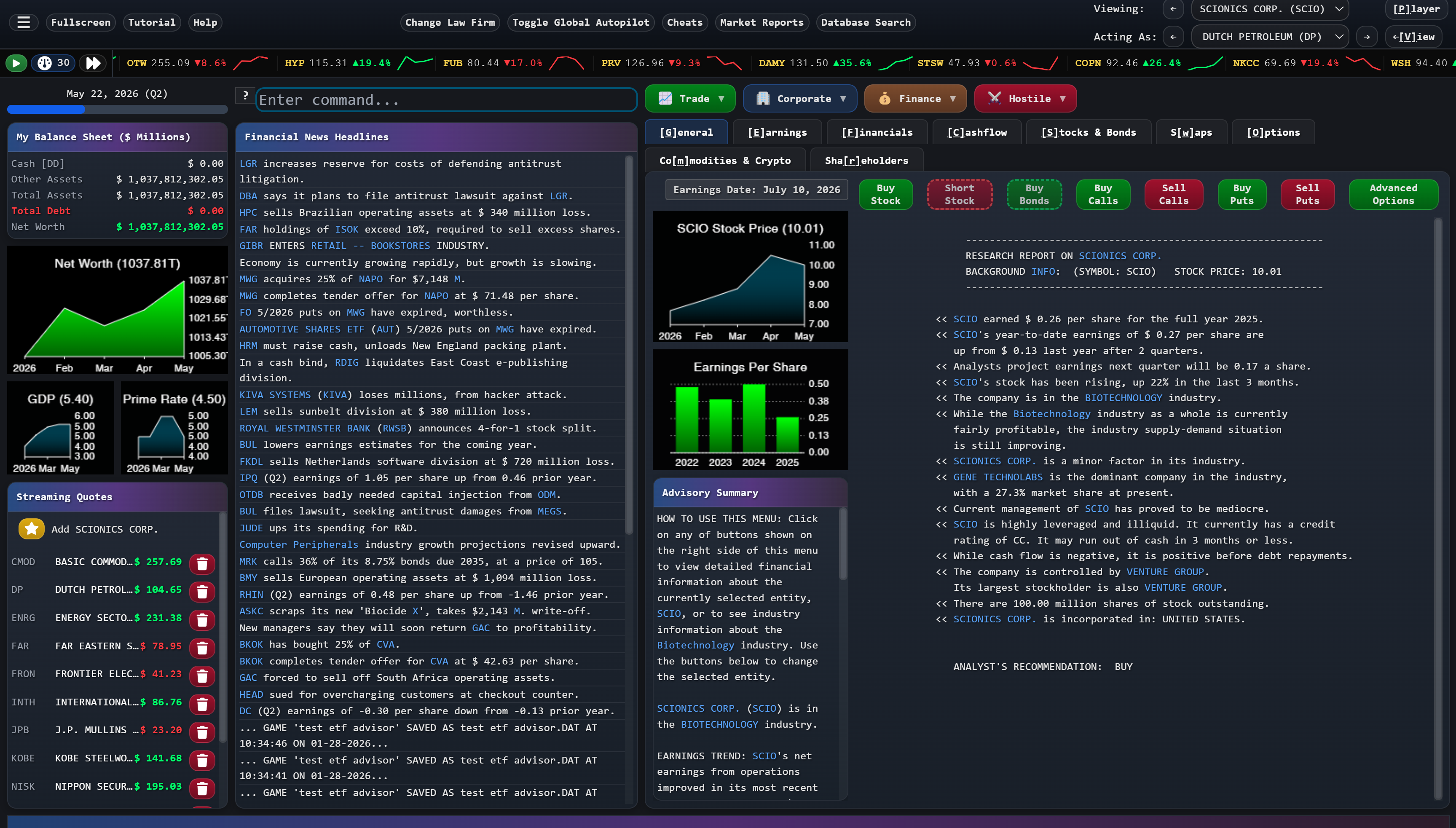
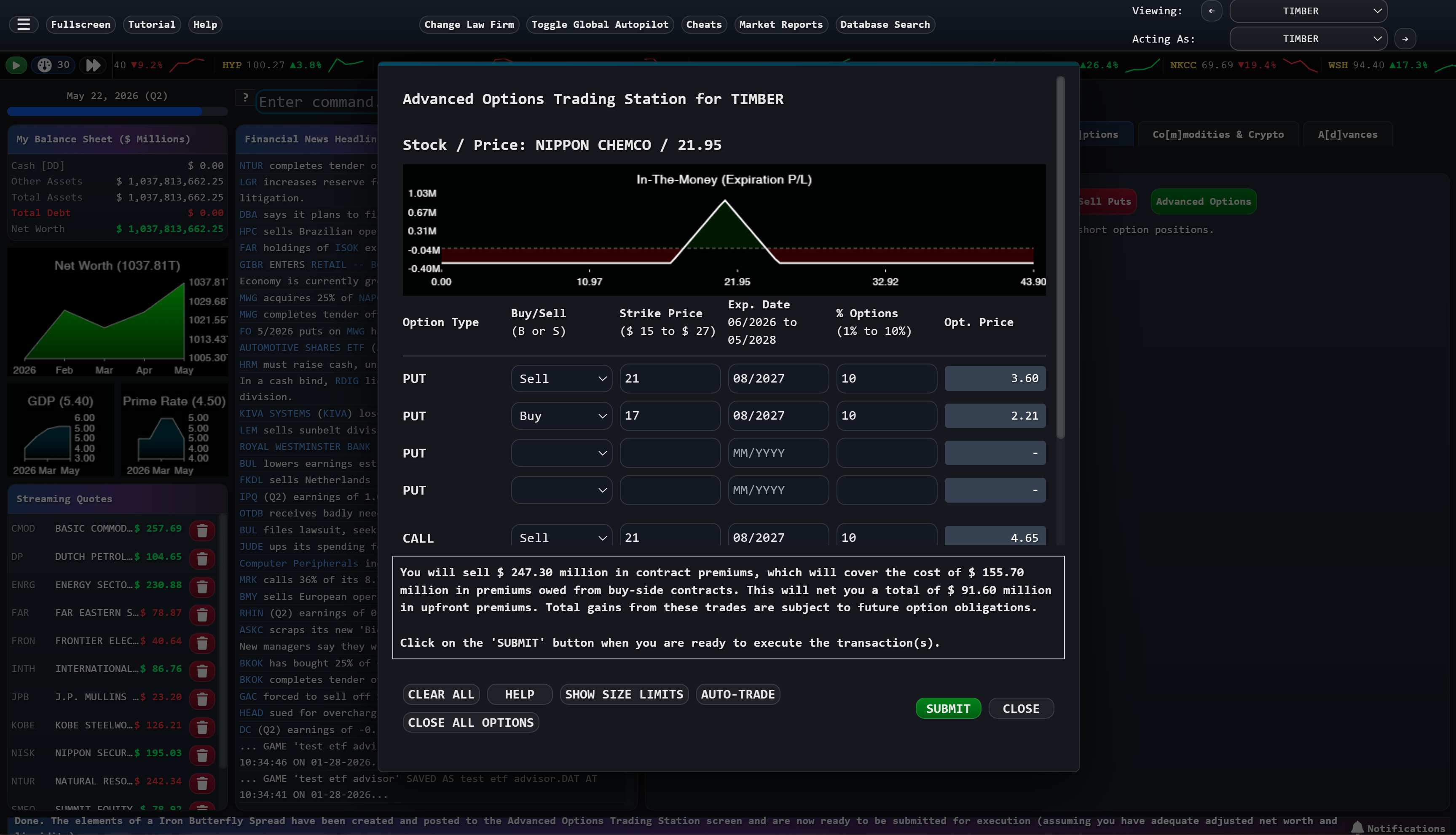
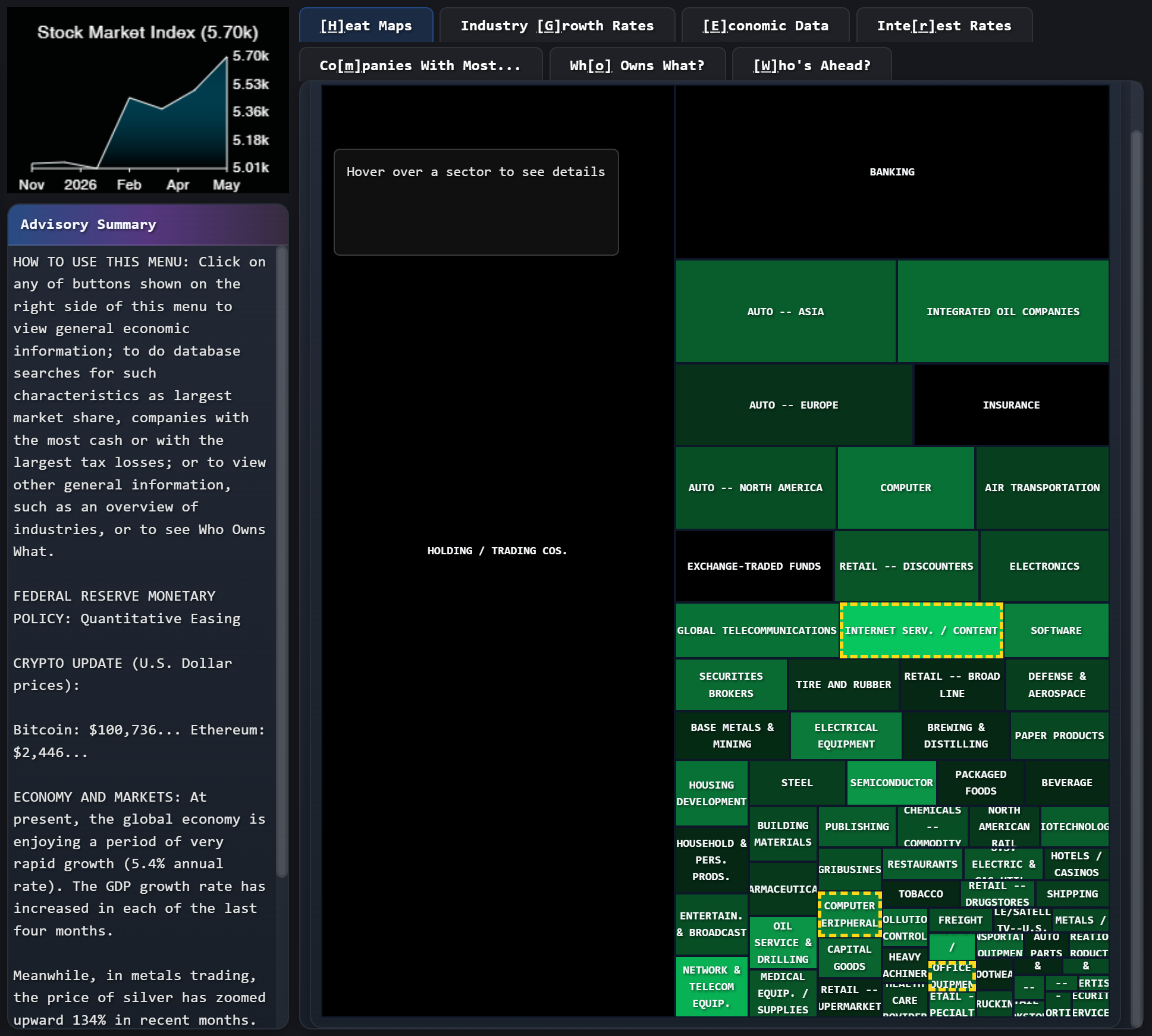
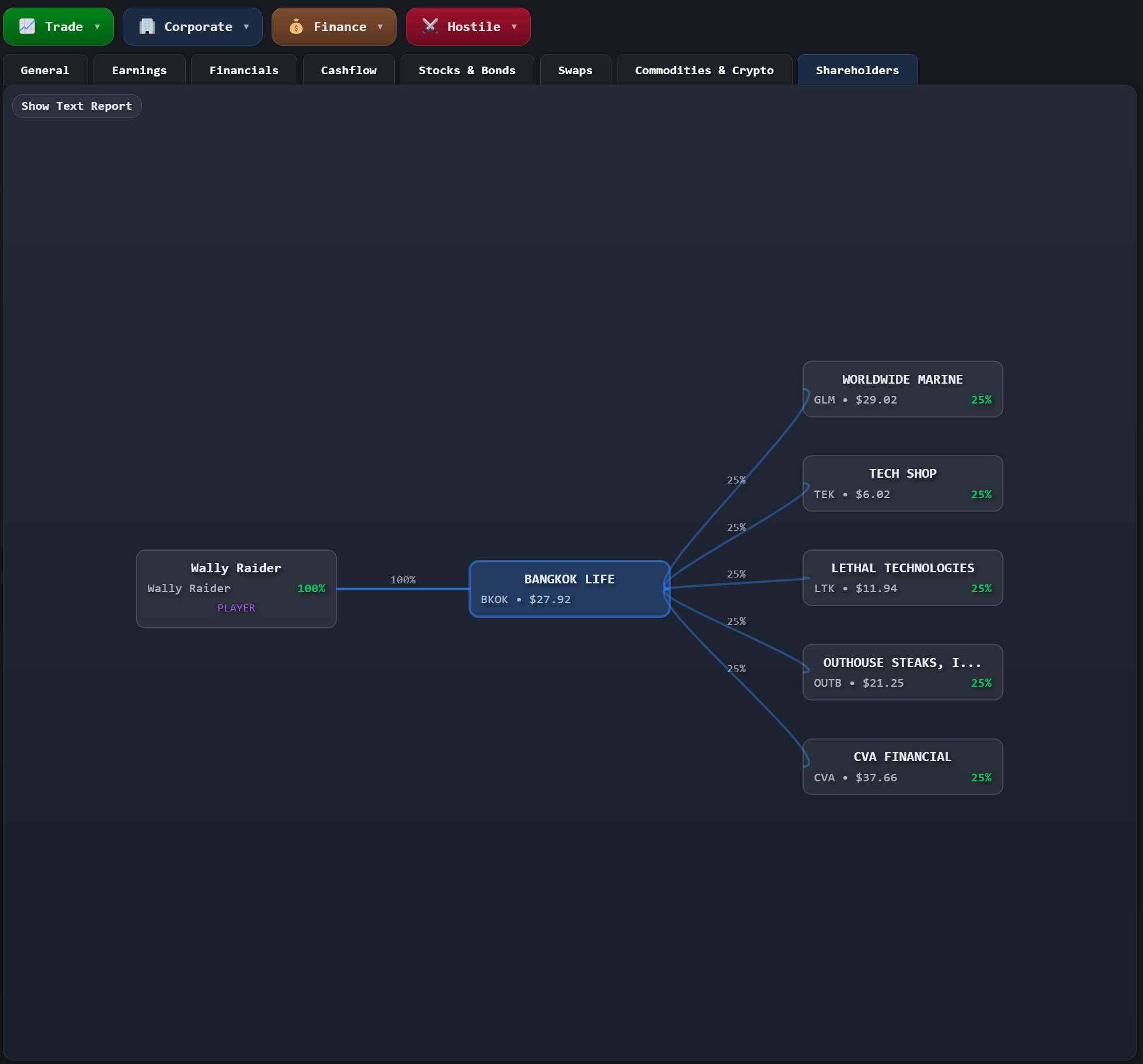
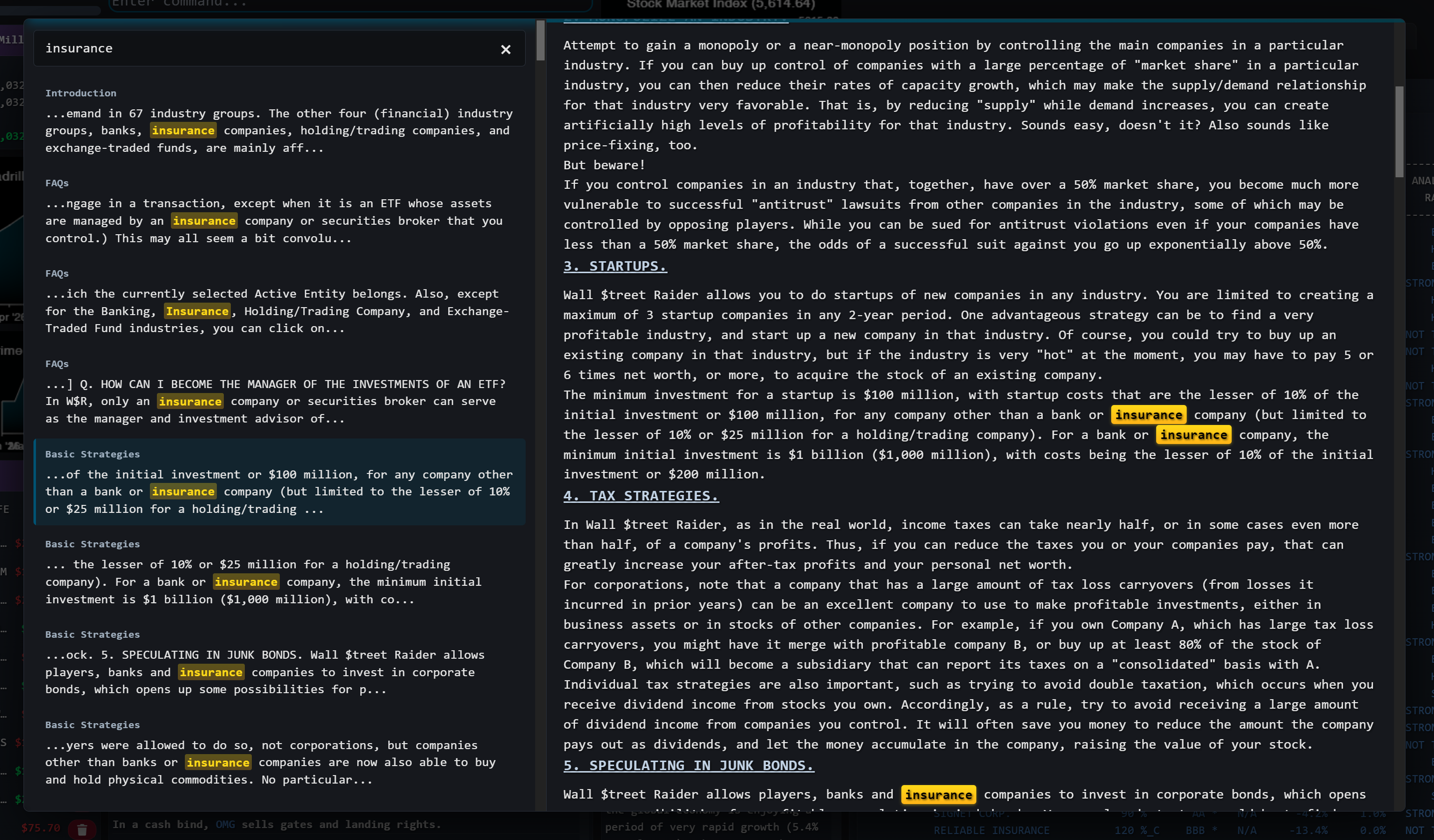
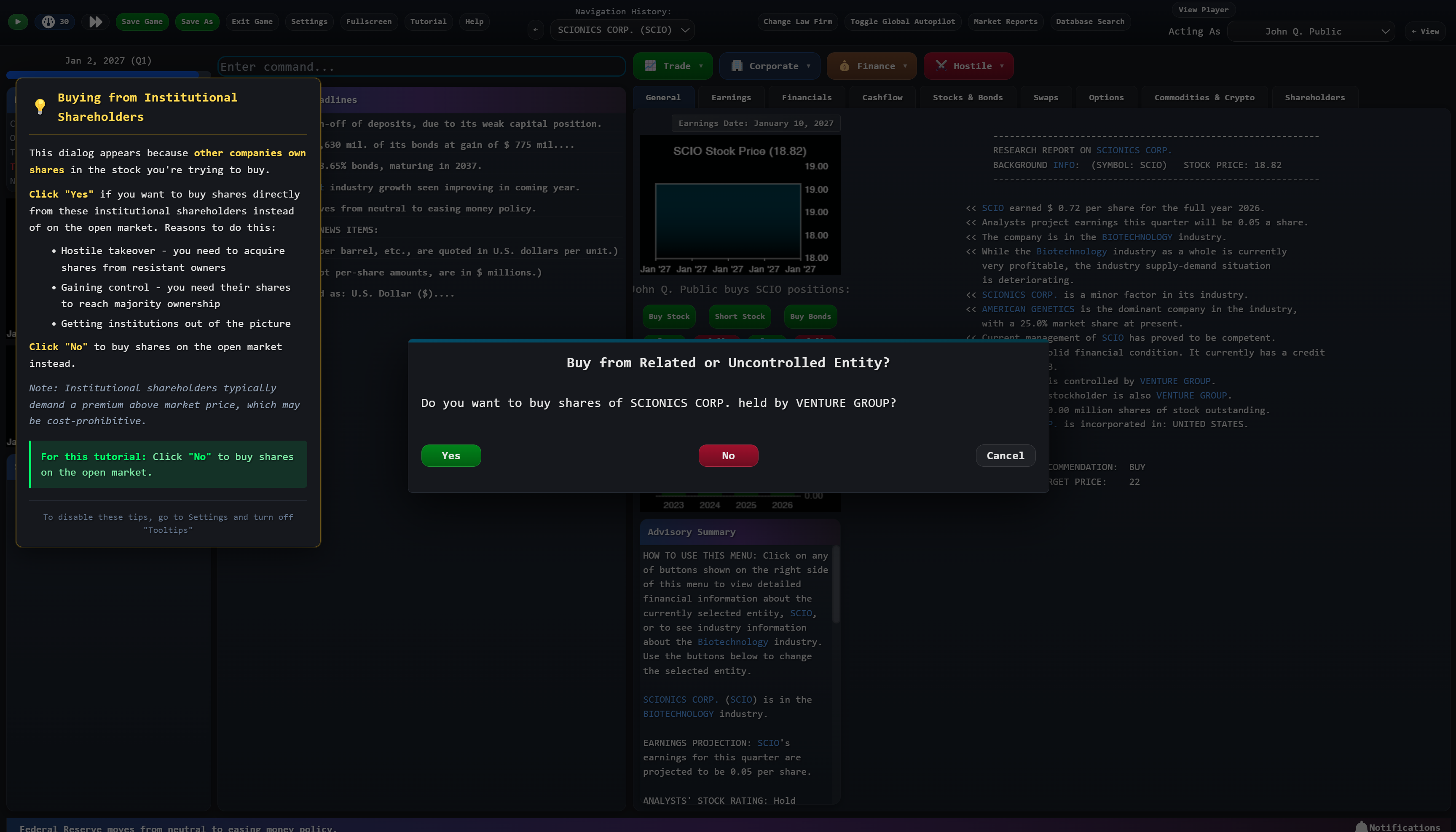
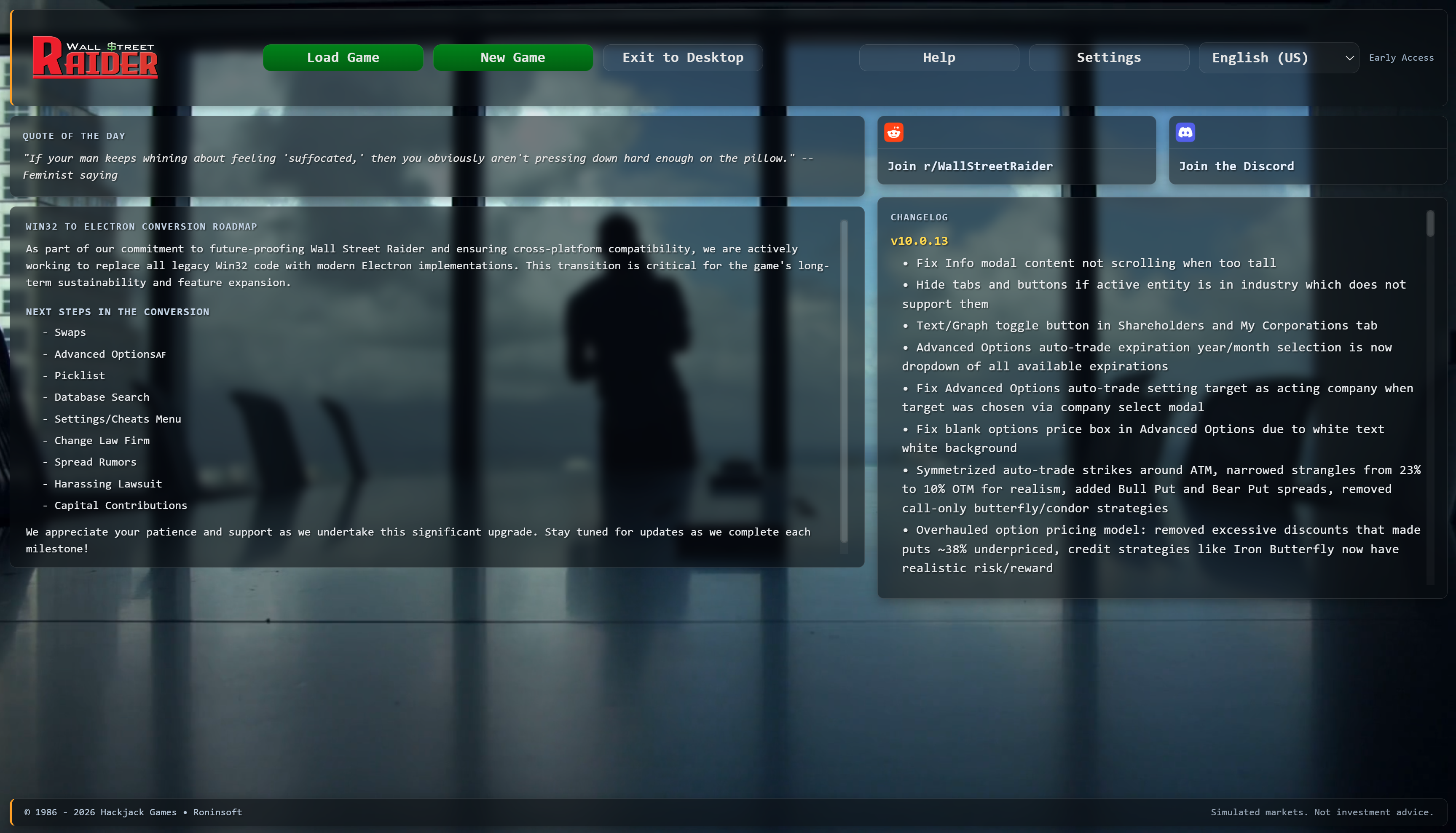
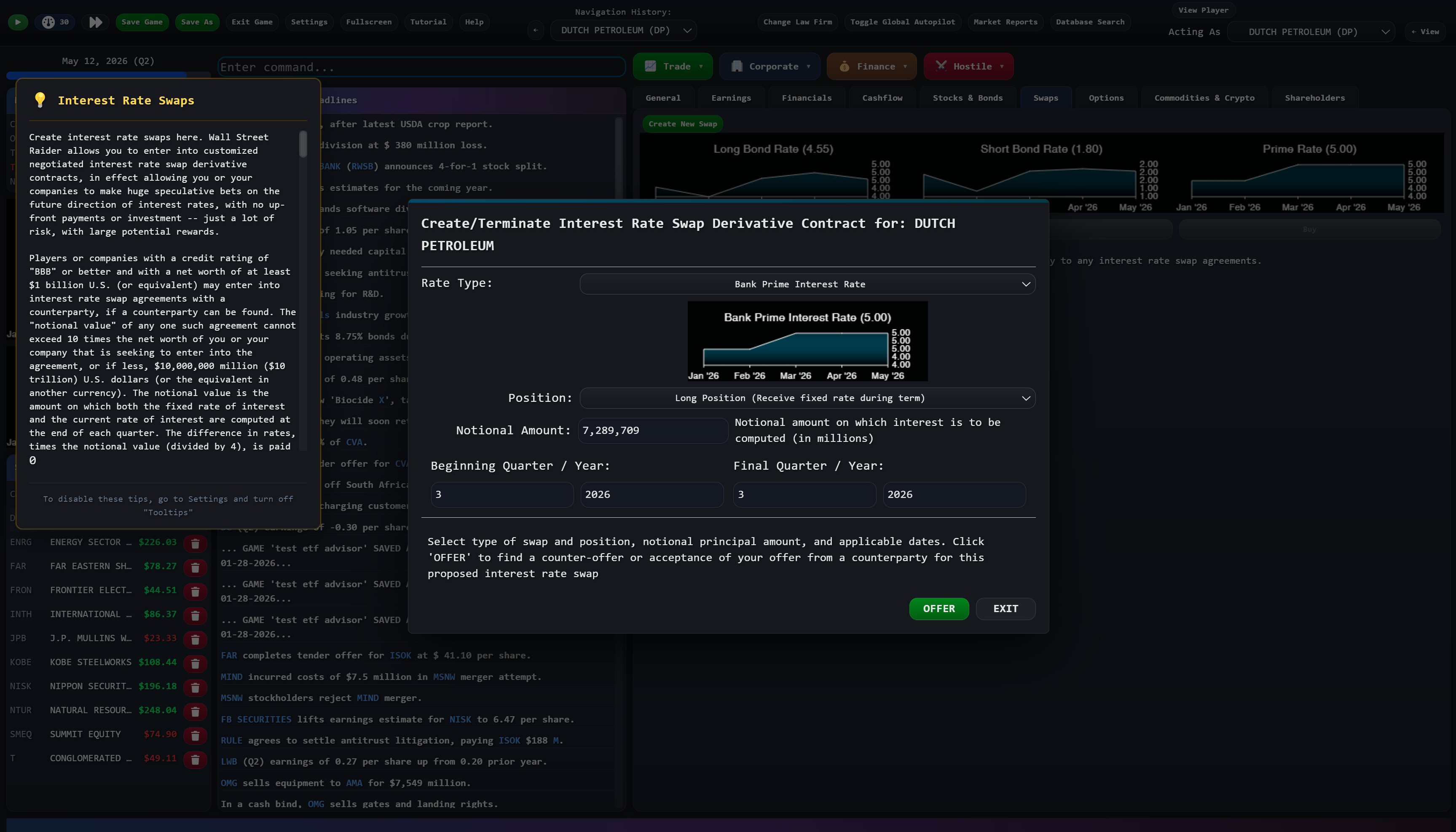
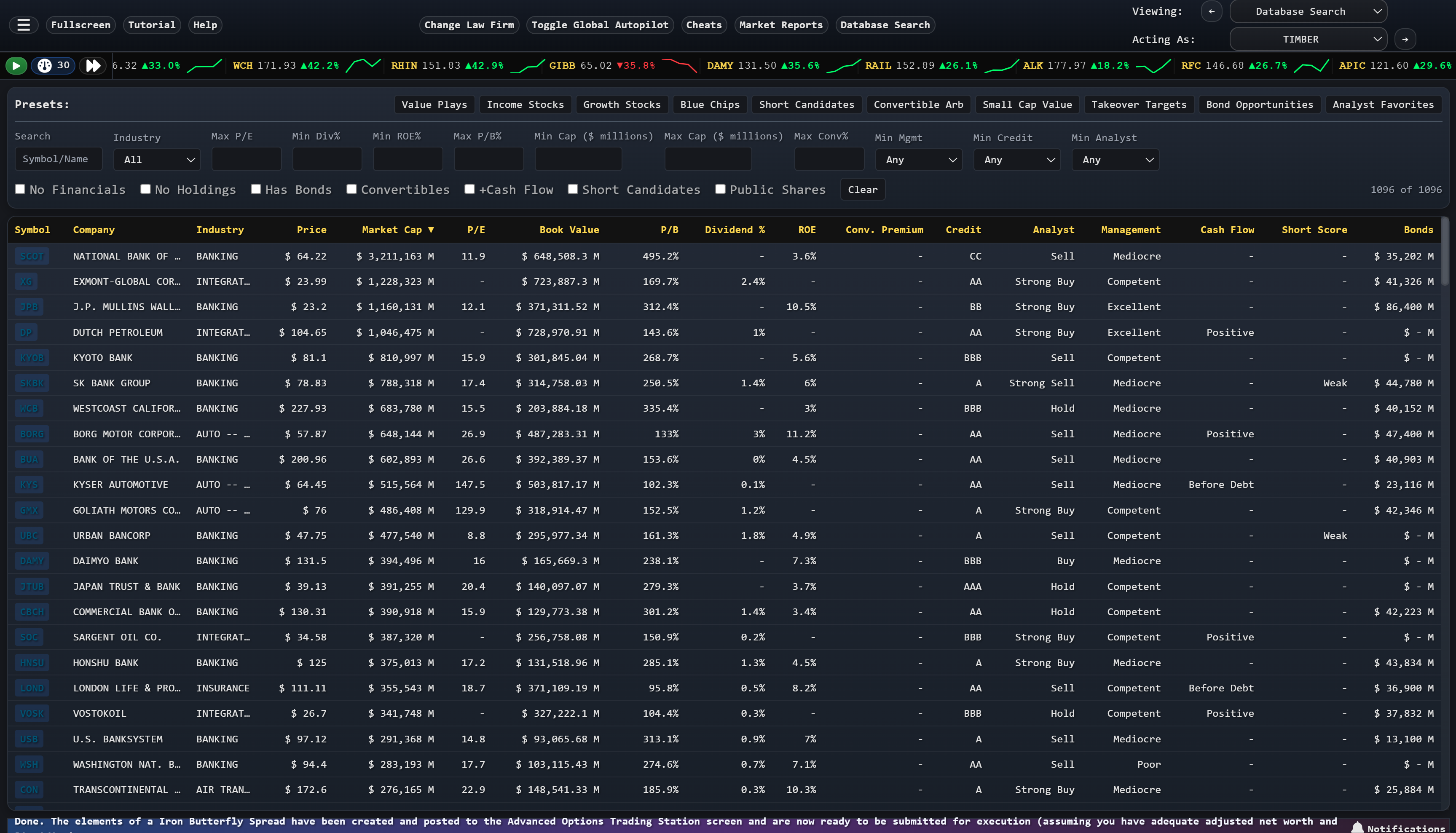
The most comprehensive financial simulation ever made. Trade stocks, bonds, options, futures, and more across 1,600 simulated companies. Now remastered for Steam.

Since 1986 • 40 years of continuous development
The most comprehensive financial simulation ever made. Trade stocks, bonds, options, futures, and more across 1,600 simulated companies. Now remastered for Steam.
, these files do not undergo rigorous security audits. They frequently contain:
from unofficial sources poses a severe security threat. Unlike software from verified developers
The modern digital landscape is defined by the ease of information exchange, yet this convenience is shadowed by the proliferation of unverified executable files and scripts. A prominent example is the recurring appearance of "v7" iteration ZIP archives across various gaming and software communities. While these files often promise enhanced performance or "cheats," they represent a significant intersection of cybersecurity risk and digital ethics. 1. Security Vulnerabilities and Malware Downloading compressed archives like
In gaming communities, "rz" often refers to "Regedit" (Registry Editor) tweaks. Users seek these to modify system settings for a perceived advantage, such as reduced latency or improved "aim." However, manually modifying the Windows Registry using unknown scripts is hazardous. It can lead to: System Instability: rz v7.zip download
Beyond technical risks, the use of such files raises ethical questions regarding fair play and intellectual property. Utilizing third-party scripts to gain an advantage in a competitive environment undermines the integrity of the platform. Furthermore, supporting unverified distributors often funnels traffic toward sites that profit from piracy or data theft, harming the original creators and the broader software ecosystem. Conclusion
Encrypted payloads that can lock a user's data until a payment is made. 2. The "Regedit" and Scripting Phenomenon
The Ethics and Risks of Unofficial Downloads: A Technical Perspective , these files do not undergo rigorous security audits
Scripts designed to record keystrokes, potentially compromising sensitive data like bank credentials or passwords. Ransomware:
far outweigh the potential benefits. Users are encouraged to utilize official support channels, such as the Seattle Services Portal for specific local services or official software repositories
Malicious code disguised as legitimate software that grants unauthorized access to a user's system. Keyloggers: A prominent example is the recurring appearance of
Official game clients often detect these modifications as "cheating," leading to permanent account bans. 3. Ethical Considerations
Incorrect registry values can cause frequent crashes or prevent the operating system from booting entirely. Voided Software Integrity:
See It In Action
What People Say
"An 'imaginative, stimulating' business simulation."— Investors Business Daily (front page article)
"I've been playing your game since I was 13 years old. Couldn't even afford to buy the full version. So I played the two-year version for years and years. And it taught me so much that now I'm working for Morgan Stanley as a forex trader in Shanghai."— Wall Street Raider player
"It's like the Dwarf Fortress or Aurora 4X of the stock market. There really is nothing like it on the market."— Outsider Gaming
"I've seen the source code of the game and I still can't beat it."— Ben Ward, Lead Developer (Steam remaster)
Watch
Ready?
The most realistic Wall Street simulation ever made is coming to Steam.