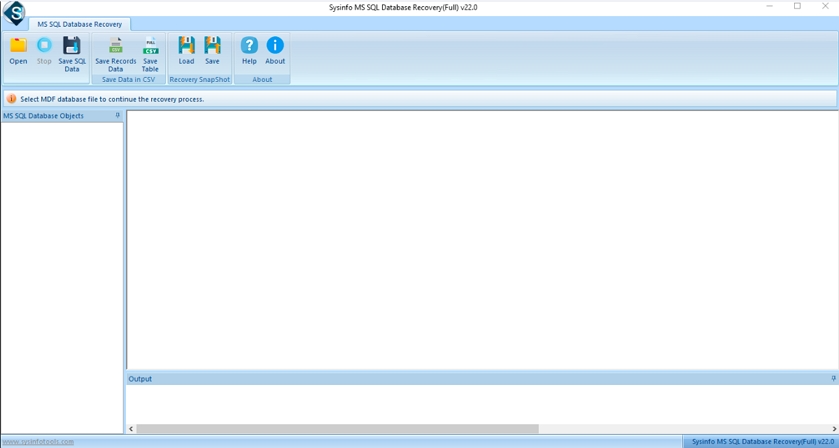
Step-1: Launch SQL Recovery Software as an administrator on your device.
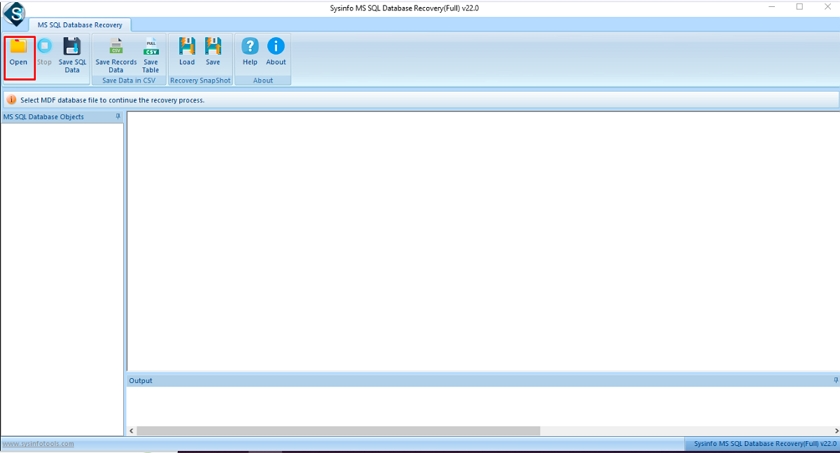
Step-2: Click on the Open button and select the corrupt MDF file. k-dat tool
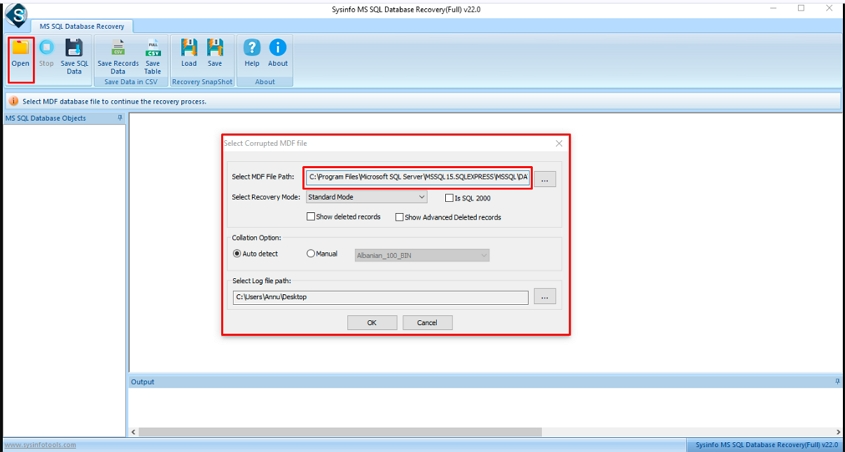
Step-3: After that, check the path of the added MDF file.
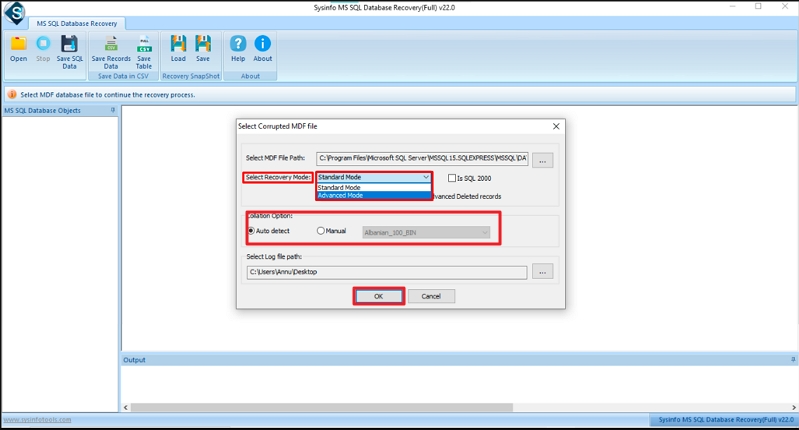
Step-4: Select Recovery Mode as Standard or Advanced and choose the Collation option. Click OK. Traditional user-land tools (like ps , lsof ,
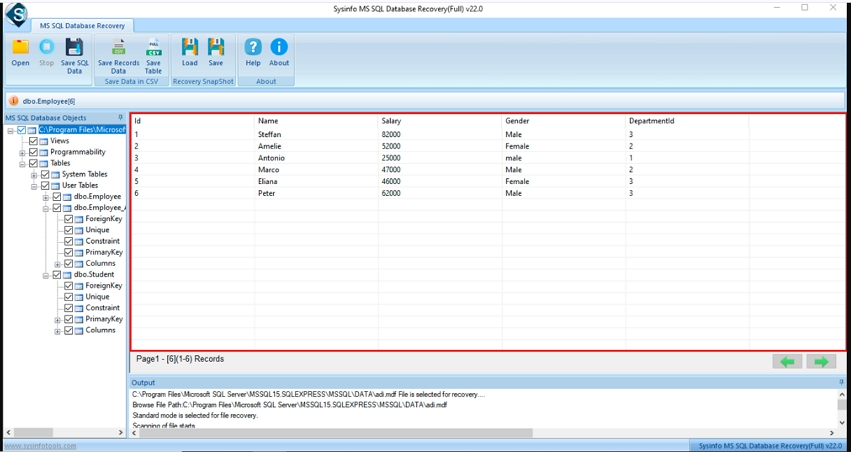
Step-5: Preview the Files, Folders, or Subfolders of the corrupted file and select the database object.
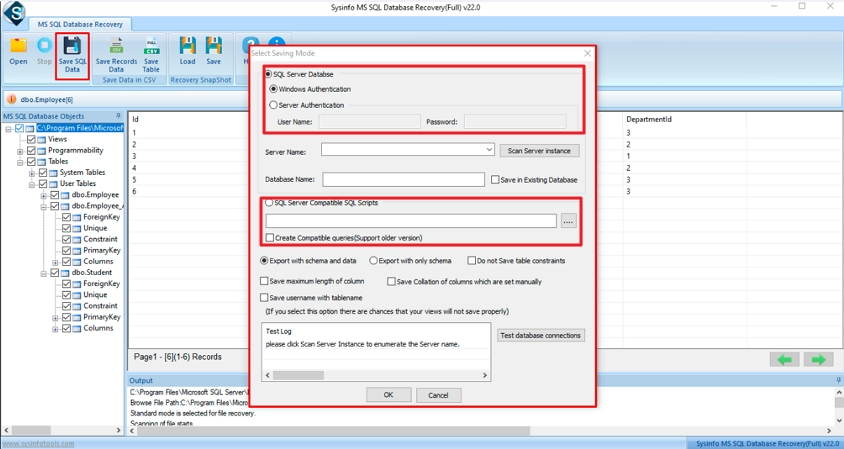
Step-6: Now, you can choose options for saving recovered files either SQL Server Database or SQL Server Compatible Scripts. Click the OK button. The tool’s name implies Kernel Data Assurance Tool
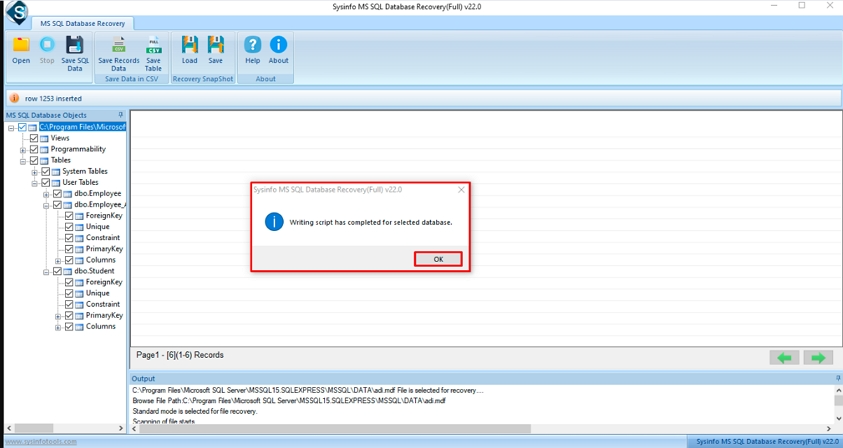
Step-7: Finally, a pop will disappear on your screen as the process is completed, click on the OK button.