- Client Taleemify
- Project Type Courses Portal
- Date 15 March, 2024
- Live Link https://taleemify.pk/
Taleemify - Online & Offline Courses Portal
Project Info
ISO 27008 is an international standard published by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC). The standard provides guidelines for the review of information security controls, including the processes and procedures for assessing the effectiveness of an organization's information security controls.
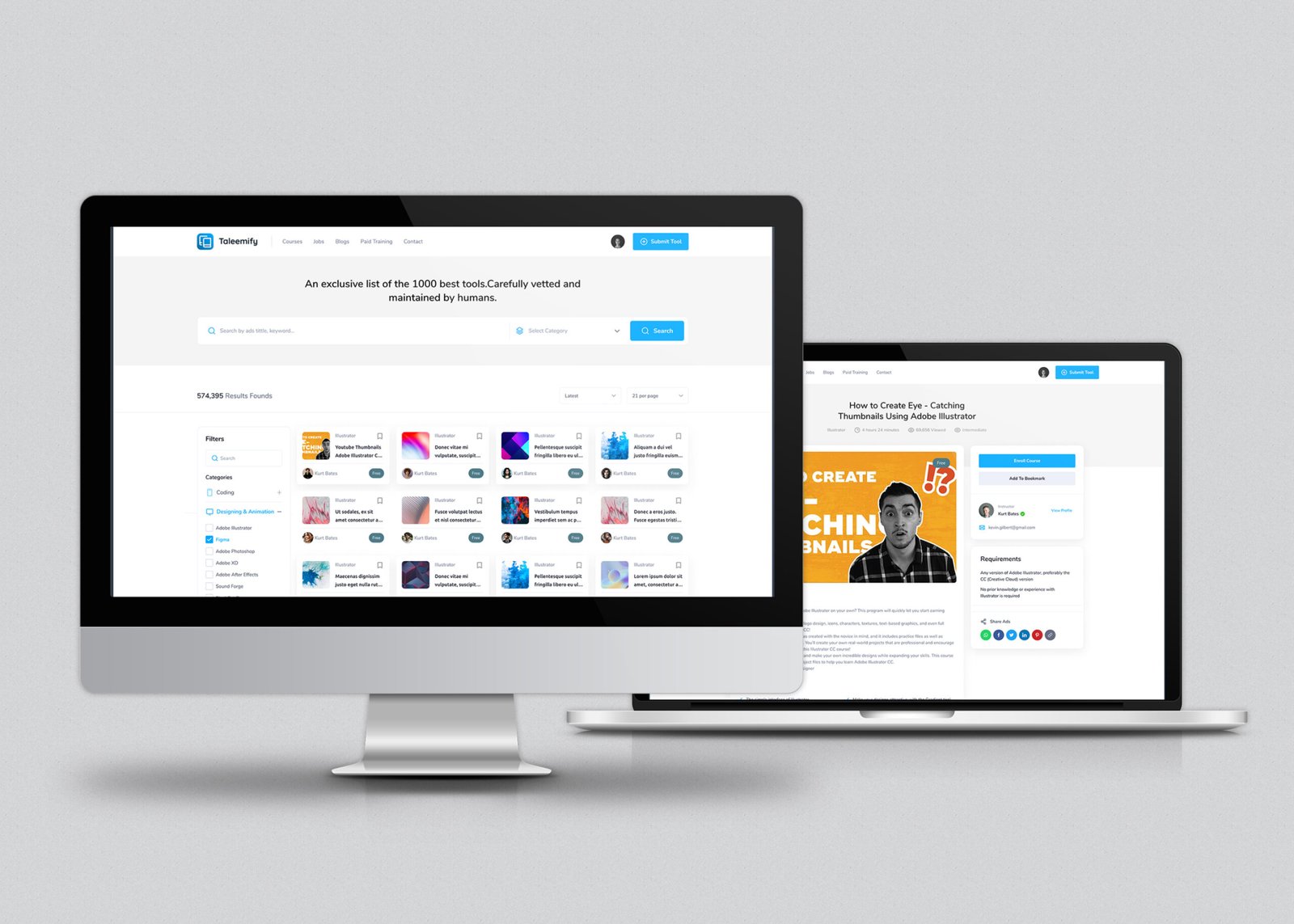
Responsive Design:
Recognizing the importance of accessibility across devices, we created a responsive design that delivers a consistent user experience on desktops, tablets, and mobile devices. This ensures that users can explore courses and make decisions no matter where they are.
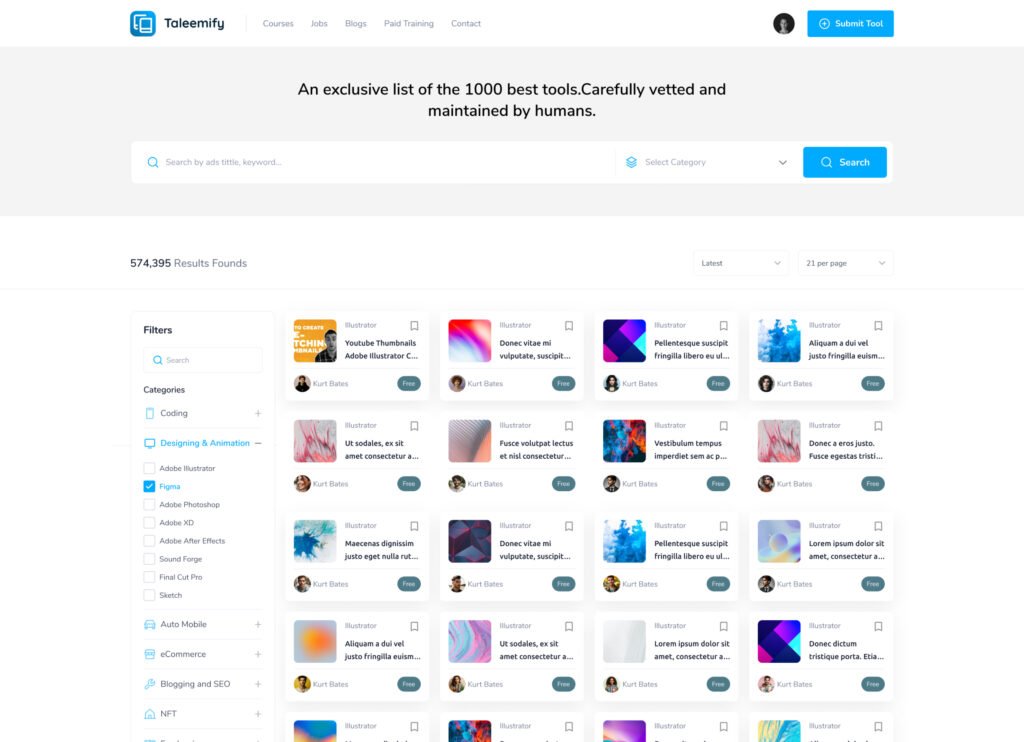
Visual Consistency:
The visual design is consistent with the brand identity of Taleemify.pk, using a color scheme and typography that reflects the platform’s educational focus. The UI design combines modern aesthetics with functionality, creating an engaging and professional feel.
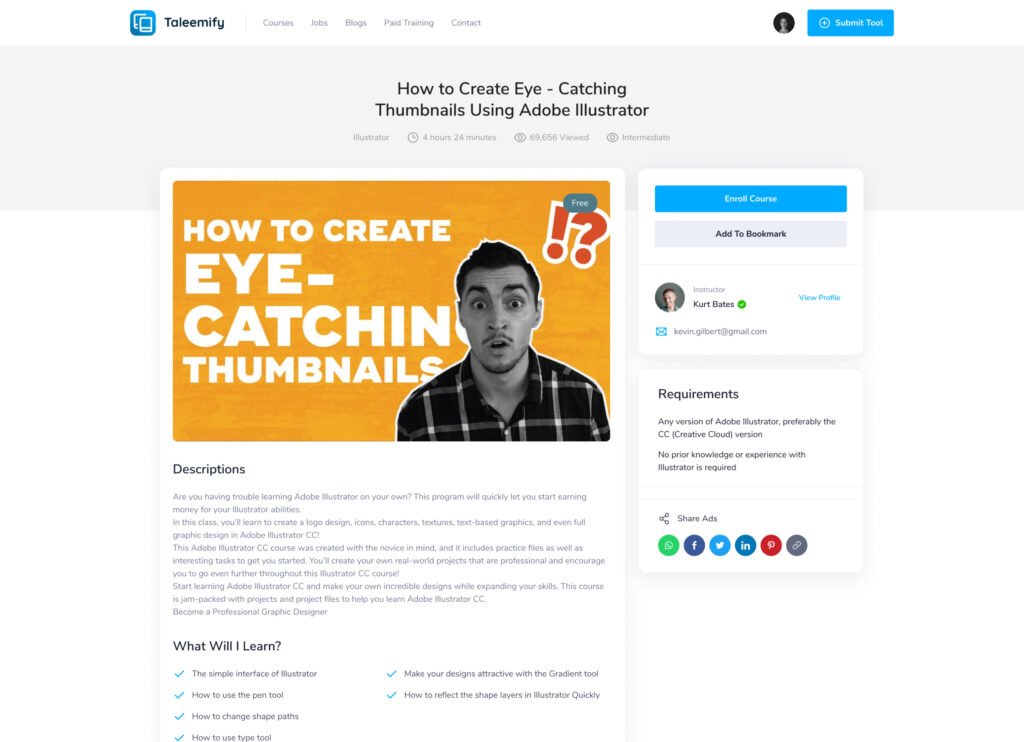
Call-to-Action Optimization:
To encourage user engagement, we strategically placed call-to-action buttons throughout the site. These are designed to guide users towards exploring more courses, saving favorites, or starting their learning journey immediately.
At Cresol360, our expertise in UI design was instrumental in shaping the user experience of Taleemify.pk. By focusing on clarity, ease of use, and visual appeal, we helped create a platform that effectively connects users with the courses they need to advance their education and careers.